[Update] Deception.Pro May 2026
AI Reports, Telemetry Timelines, and Deeper AD Realism
We've shipped a substantial round of improvements across the Deception.Pro platform, focused on three things our customers ask for most: faster time-to-insight, higher fidelity decoy environments, and more usable telemetry artifacts. Here's what's new.
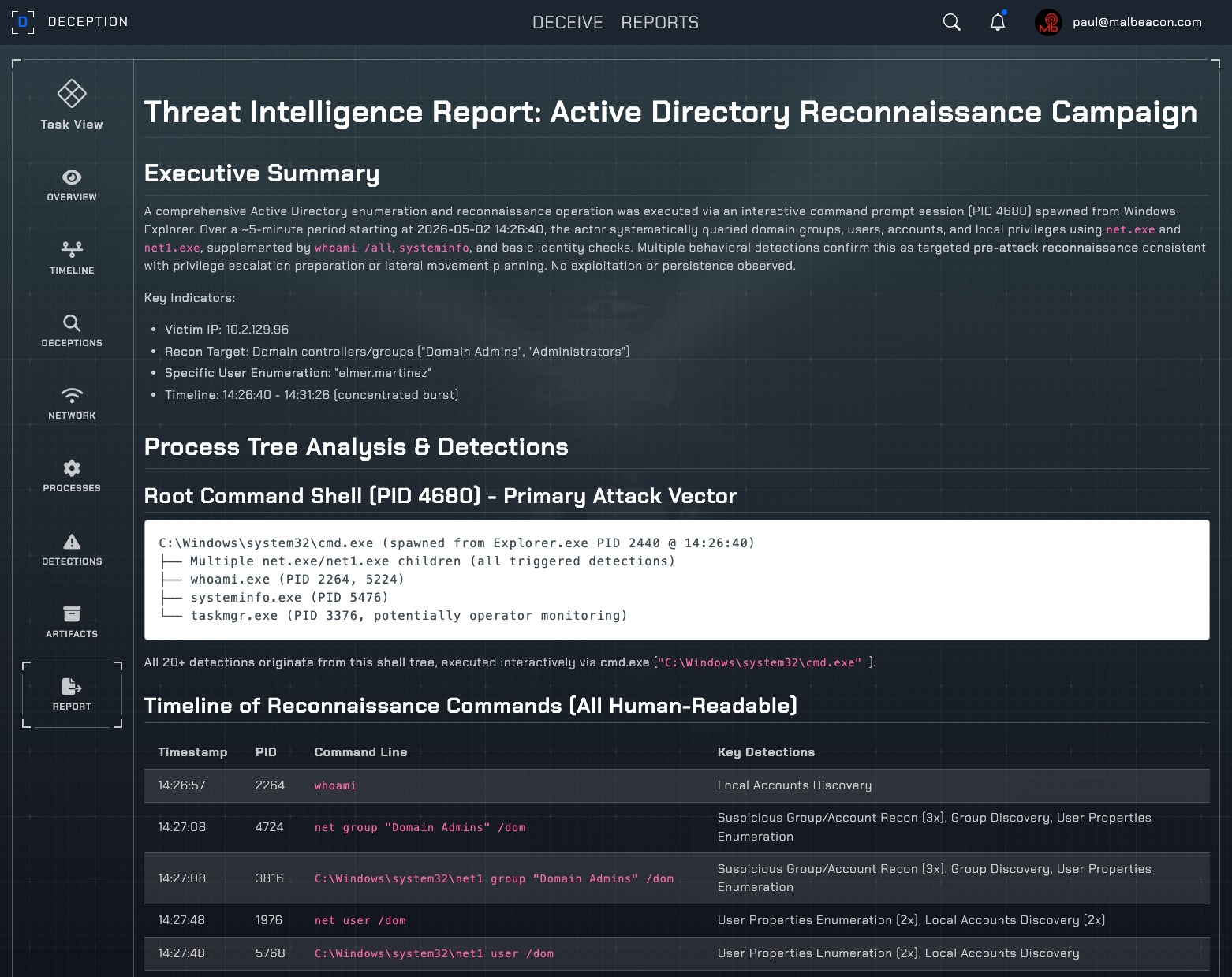
Screenshot of Deception.Pro's AI-generated threat intelligence report, summarizing adversary behavior, indicators, and TTPs.
Why This Matters
Every improvement feeds the same outcome: higher-quality, more defensible adversary telemetry. AI reports compress analyst hours into minutes. Timeline-correlated EDR and network artifacts cut investigation time and produce cleaner training data for detection engineering and AI SOC pipelines. These realism upgrades including randomized timestamps, expanded AD, and VPN-aware timezones keep adversaries engaged longer, which means deeper TTPs captured per session and richer datasets per dollar spent. For teams licensing our telemetry, that translates directly to more behavioral coverage per record. For teams running their own deception operations, it means less time tuning environments and more time extracting value from what adversaries actually do inside them. If you're evaluating Deception.Pro, this is the floor, not the ceiling.
Frontend
AI-Generated Reports (Paying Customers)
Every paying customer can now generate AI reports directly from the platform. Point Deception.Pro at a completed deception operation and get a structured writeup — adversary behavior, indicators, TTPs, exfil paths — in minutes.
EDR & Network Timeline in Artifact Downloads
Artifact downloads now include a chronologically ordered timeline of EDR telemetry and network connections. Analysts and detection engineers can correlate process events to network activity without stitching together separate exports.
System-Generated File Filtering in Artifacts
New filtering distinguishes system monitoring artifacts from OS file system modifications.
Backend
Timestamp Randomization on Replica Files
Replica documents and decoy files now carry randomized creation, modification, and access timestamps. The result: deception environments that hold up under scrutiny from threat actors who check filesystem metadata for tells.
Faster Environment Initialization
We've cut environment spin-up time significantly. Operators can stand up new honeynets and rotate environments faster — important when running concurrent operations or burning a compromised decoy.
Improved File Cleanup
Cleanup routines between operations are tighter. Less residue, fewer artifacts carried over between runs, cleaner per-operation telemetry.
Faster Chrome Credential Injection
Seeded and tracked credentials now inject into Chrome faster. Honeytoken accounts are in place and ready to be harvested as soon as the environment comes online.
Expanded Deception AD
Active Directory environments now ship with more user accounts, groups, machine objects, and organizational structure. Larger, more believable AD topologies reduce the chance an adversary recognizes the environment as a decoy during enumeration.
VPN-Based Timezone Configuration
Honeypot timezone is now set automatically based on the VPN egress location. A decoy routing through a German VPN now reports a German timezone — small detail, big credibility gain against TAs who check.
Get Started
As always — questions, issues, or feedback, reach out directly. Happy hunting, hackers!
— Deception.Pro Team