[Update] Deception.Pro April 2026
TLS Introspection is Live!
This is the one you've been asking for.
TLS introspection is now available across all Deception.Pro operations. Decrypted PCAPs are generated automatically and deposited directly into the Artifact section of each operation — giving you full plaintext visibility into encrypted adversary traffic for the first time.
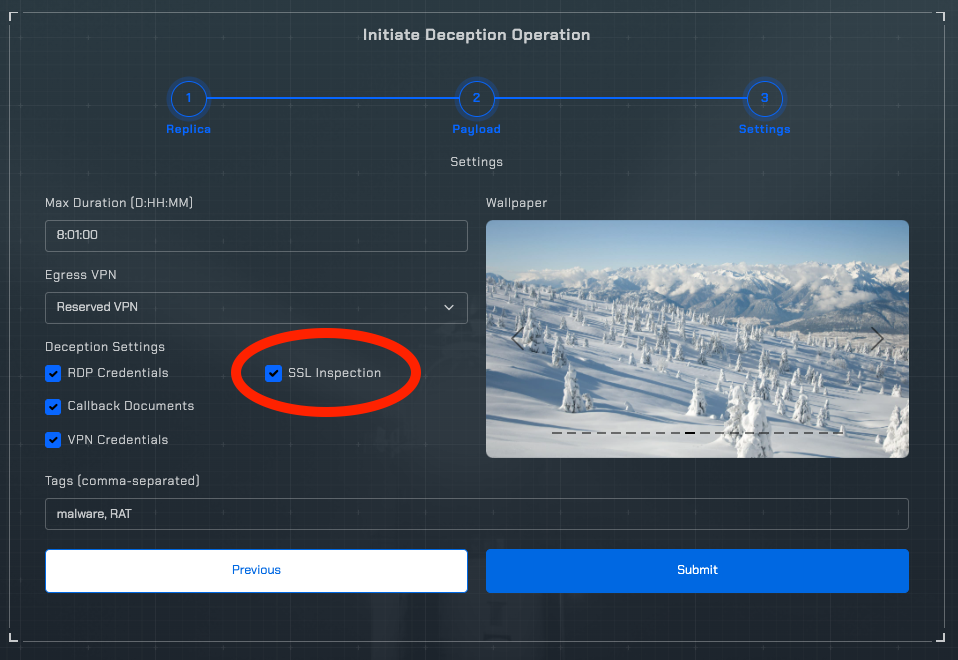
The SSL Inspection (to include TLS) checkbox is now enabled by default during operation initiation!
Why This Matters
Modern threat actors rarely operate in the clear. C2 beaconing, credential exfiltration, lateral movement tooling — virtually all of it runs over TLS. Until now, PCAPs from deception operations captured the shape of encrypted sessions but left the content opaque.
That changes today.
With TLS introspection enabled at the operation level, Deception.Pro now captures and decrypts session traffic in real time. The resulting decrypted PCAPs land in the Artifact section alongside your EDR telemetry, Suricata EVE logs, and raw captures — giving you a complete, correlated picture of adversary behavior from network to endpoint.
What's in This Release
TLS Introspection + Decrypted PCAPs
The headline feature. Available now on all active operations. Check the Artifact section.
Faster Network and Artifact Delivery
Telemetry and artifacts surface faster after capture. If you've noticed latency between an event and its appearance in the platform, you should see a meaningful improvement.
Stability and Internal Architecture Improvements
A large set of changes that don't make for exciting patch notes but matter a lot in practice — improved reliability, cleaner internal structure, and a more resilient platform overall.
An Apology
We owe you one.
Getting TLS introspection right took longer than expected, and the debugging process caused extended platform downtime. That's not a tradeoff we made lightly, and we know downtime has a real cost when you're running live operations. We're sorry for the disruption, and we've put additional safeguards in place to prevent that kind of impact going forward.
Get Started
Decrypted PCAPs are available now. Log in, start a new deception operation, and check the Artifact section.
As always — questions, issues, or feedback, reach out directly. Happy hunting, hackers!
— Deception.Pro Team