[Update] Deception.Pro March 2026
This release brings a major new visibility tool for detonation analysis, expanded YARA detection coverage, platform stability improvements, and a transparency update regarding telemetry handling for free researcher accounts.
..:: New Feature ::..
Timeline View - Full Process and Network History at a Glance
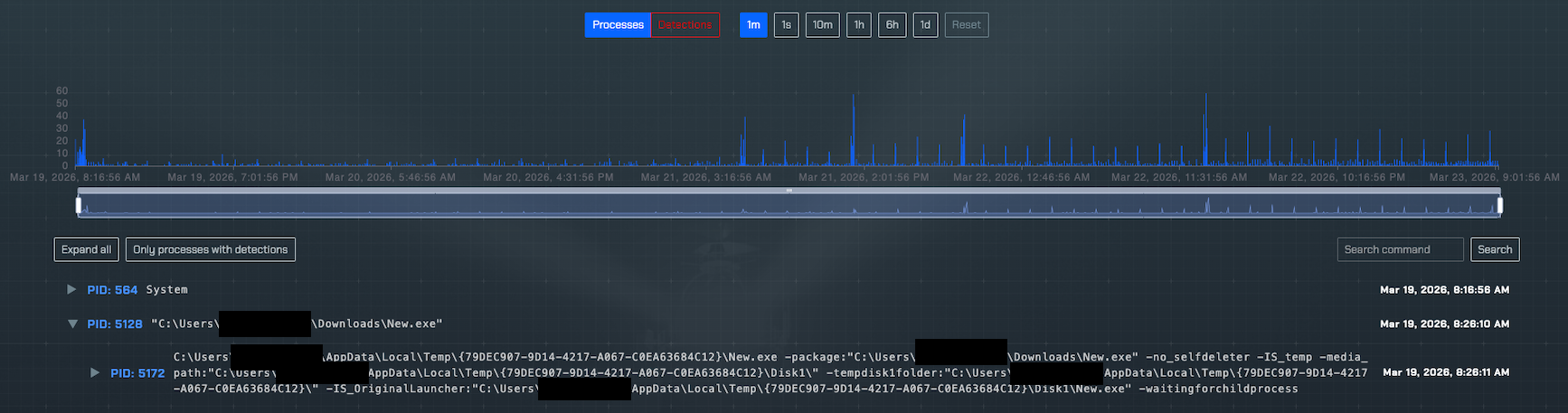
The new Timeline View gives you a single, unified process tree across the full duration of a detonation — not just a static snapshot. Network connections, new file writes, and detection events are all surfaced in one scrollable, filterable chronology, so you can follow an intrusion the way it actually unfolded rather than stitching together disconnected point-in-time views.
Example image of Timeline View from an actual operation.
The timeline chart doubles as an interactive filter — click any event type or drag to select a timespan and the tree updates instantly. Timelines have been retroactively generated for all previously submitted tasks and will continue updating in real time for any active detonations currently running.
..:: Bug Fixes ::..
Several bugs affecting UI stability and rendering performance have been resolved. These fixes address edge cases that caused inconsistent state across views, stale data on page transitions, and latency in rendering large process trees. The interface should feel noticeably more reliable across the board — particularly for tasks with high event volumes or extended detonation windows.
..:: Policy Update ::..
Telemetry Consent for Free Researcher Accounts
Free researcher accounts will now be asked to consent to their anonymized operational telemetry being used to train AI detection models. This data helps us improve automated analysis and detection quality over time. This applies only to free researcher accounts. Paid accounts and any active Proof of Value engagements are entirely unaffected.
..:: Improved YARA Coverage ::..
YARA scanning has been significantly improved for malicious code both in memory and on disk. Detection accuracy is higher across packed, obfuscated, and reflectively-loaded PE files, reducing missed detections on common evasion techniques used during post-exploitation. These improvements are applied automatically — no rule changes are needed on your end. Existing tasks will reflect updated detection results on next analysis.
..:: Questions or Feedback ::..
Reach out via the in-platform support channel or contact your account team directly. If you're on a free researcher account and have questions about the telemetry consent flow, we're happy to walk through exactly what's collected and how it's used.
..:: Future Happenings ::..
Attackers bet heavily on encryption to blind defenders — that's about to get harder. TLS introspection is on the near-term roadmap, bringing full visibility into encrypted channels inside deception environments. It's one of several major capabilities coming across detection, analysis, and deception infrastructure. Watch this space.
Happy hunting!
~ Deception.Pro Staff